This article introduces Tair-KVCache-HiSim, a high-fidelity CPU-based simulator for optimizing multi-tier KV Cache configurations in LLM inference.

This article introduces using Alibaba Cloud DAS and SLS to build a proactive, time-series audit system for preventing and governing Redis Big Keys and Hot Keys.

This article introduces hierarchical sparse attention: the full KV Cache is stored on the CPU, while the GPU keeps only a Top-k LRU Buffer.
This article introduces a dual memory-pool inference framework enabling efficient hybrid Transformer-Mamba model execution by resolving conflicting caching mechanisms.

April 2026 brought a strong wave of AI-native capabilities across Alibaba Cloud database portfolio. Highlights include Lindorm AI Engine for in-databa.

This article introduces engineering optimizations to 3FS—KVCache's foundation layer—across performance, productization, and cloud-native management for scalable AI inference.

This article explains how AliSQL natively supports high-density storage and efficient analysis by deeply integrating DuckDB while maintaining compatibility with the MySQL ecosystem.
AliSQL integrates DuckDB as a storage engine to add high-performance OLAP capabilities to MySQL while maintaining full compatibility.
This article introduces how PolarDB-X's physical addressing optimization lets the executor directly access data locations to eliminate redundant B+ tree traversals.

This article introduces how PolarDB materialized views eliminate on-the-fly processing to boost query performance by up to 100x.

PolarDB for PostgreSQL introduces a one-stop memory management system that combines vector and graph databases to enable AI agents with persistent, cross-session memory.

Lindorm tops VectorDBBench benchmarks with record-breaking vector retrieval performance and hybrid search capabilities.

DAS Agent enables AI-native database O&M with autonomous anomaly detection, root cause analysis, and closed-loop optimization.

This article introduces PolarDB's columnar table technology that reduces storage costs while enabling high-performance analytics for integrated lakehouse architectures.

This article introduces how Alibaba Cloud ApsaraDB Data Agent achieved dual breakthroughs in performance and user experience for AI-powered data analytics.

This article will deeply analyze the core capabilities of EventHouse and its positioning in the era of artificial intelligence.
This article introduces the analysis steps for traffic skew.

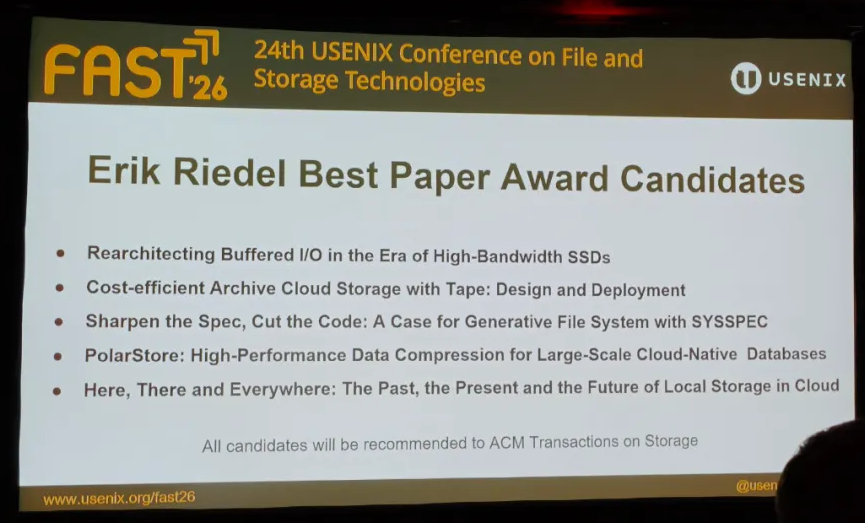
This article introduces Alibaba Cloud PolarStore's software-hardware collaborative compression architecture for cloud-native databases, which received a Best Paper Award nomination at USENIX FAST'26.
This article shares best practices to diagnose and resolve data skew.

This article introduces the enhanced features of AnalyticDB on Ray and the scheduling technology for multimodal processing.
