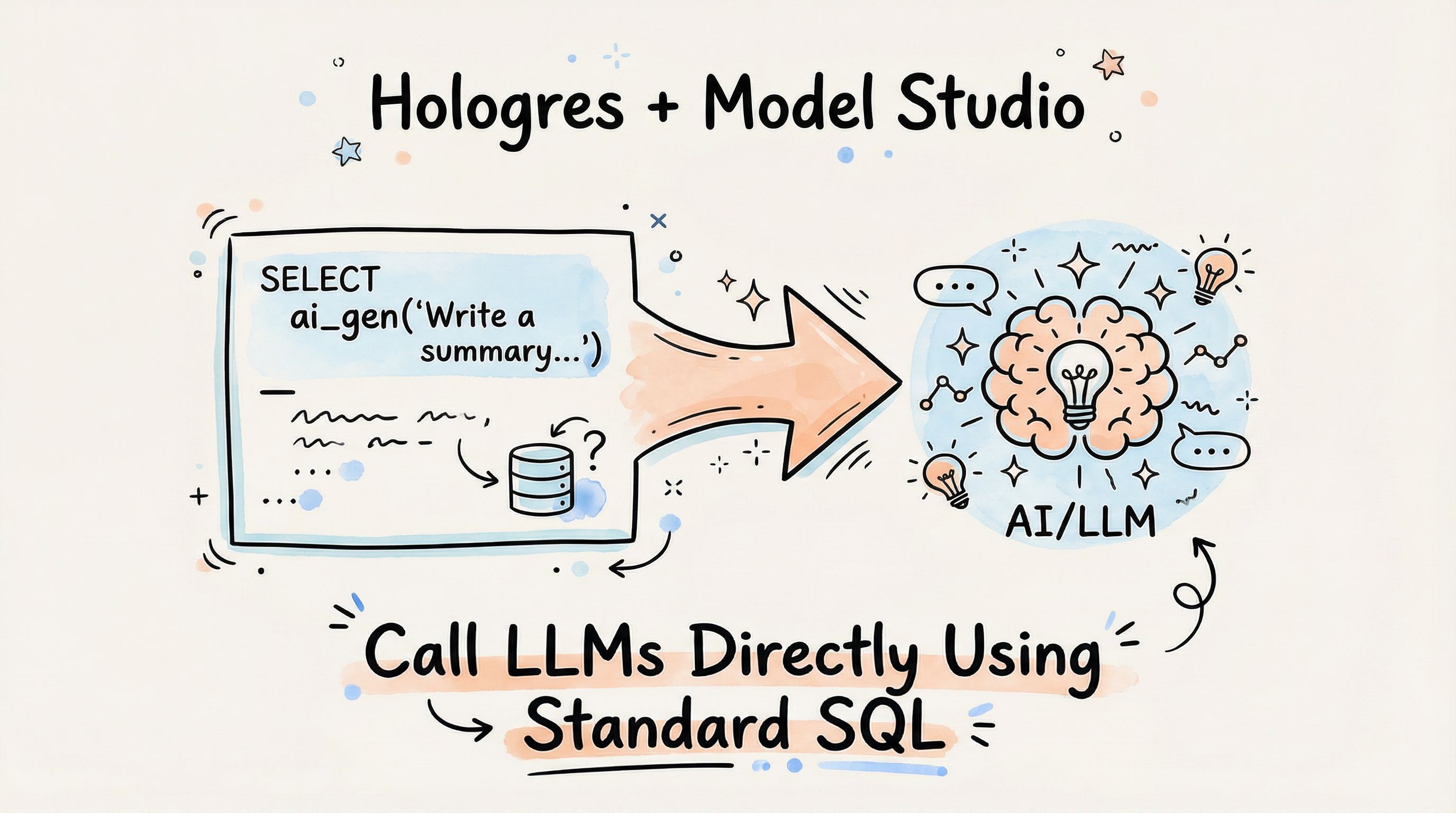
Discover how Alibaba Cloud Hologres + Model Studio lets data teams use plain SQL to call LLMs for PDF analysis, image understanding, and RAG—no GPU, Python, or AI engineering required.
In this article, we explore how to use RDS Copilot to analyze and optimize slow queries in a real e-commerce database scenario hosted on ApsaraDB RDS for MySQL.

This article provides a case study of a specific business table and describes how to design a partitioning scheme for the table step by step.

This article introduces cost-effective strategies for hosting on IaaS, focusing on different configurations for various organizational needs and scenarios.

This article introduces MaxCompute’s enhanced SQL and BigQuery-compatible features for smoothly converting and migrating 100,000 SQL statements from BigQuery.

This article introduces MaxCompute's comprehensive refactoring of its SQL execution engine to optimize complex data type processing, enabling smooth and high-performance migration from BigQuery.

This article introduces methods for obtaining and analyzing slow SQL statements in PostgreSQL and PolarDB for PostgreSQL.

This article describes the best practices for processing and analyzing JSON logs in Alibaba Cloud Simple Log Service (SLS).

Discover how Grab leverages Apache Flink for real-time analytics and data quality, transforming raw data into actionable insights.
StoreView SQL enables cross-region and cross-project data analysis within Alibaba Cloud's Simple Log Service, effectively unlocking geographical limits for data analysis.

Master Flink 2.1 SQL's AI functions with ML_PREDICT, Delta Join optimizations, and real-time AI integration for scalable stream processing applications.
This article introduces the new AutoIndex feature in PolarDB for MySQL that automates the creation of column indexes to improve query performance for complex queries in OLAP scenarios.

This article introduces two methods for executing SQL statements in batch: using the gexec convenient command in psql and using dynamic SQL.

This article mainly introduces the latest development and technical details of Alibaba Cloud OpenSearch in Text-to-SQL tasks.
This article describes how to use TRANS_ARRAY and LATERAL VIEW EXPLODE functions to transpose columns to rows in MaxCompute.
This tutorial will guide you through optimizing slow SQL in PolarDB-X.

This article introduces the application scenarios of PostgreSQL JSON and the optimization of Shared Detoast.

This article is compiled from the presentation by Ren Qingsheng, committer and PMC member of Apache Flink, at the Flink Forward Asia 2023 core technology session (Part 2).

This article outlines the SQL statement execution process, offering insights and guidance for newcomers to big data development.

Discover Flink SQL, the high-level API for executing SQL queries across streaming and batch data sets in Apache Flink.
