Quick BI Embedded Analytics delivers role-based, authentication-free report embedding for personalized, seamless data experiences.

 May 28, 2026
May 28, 2026
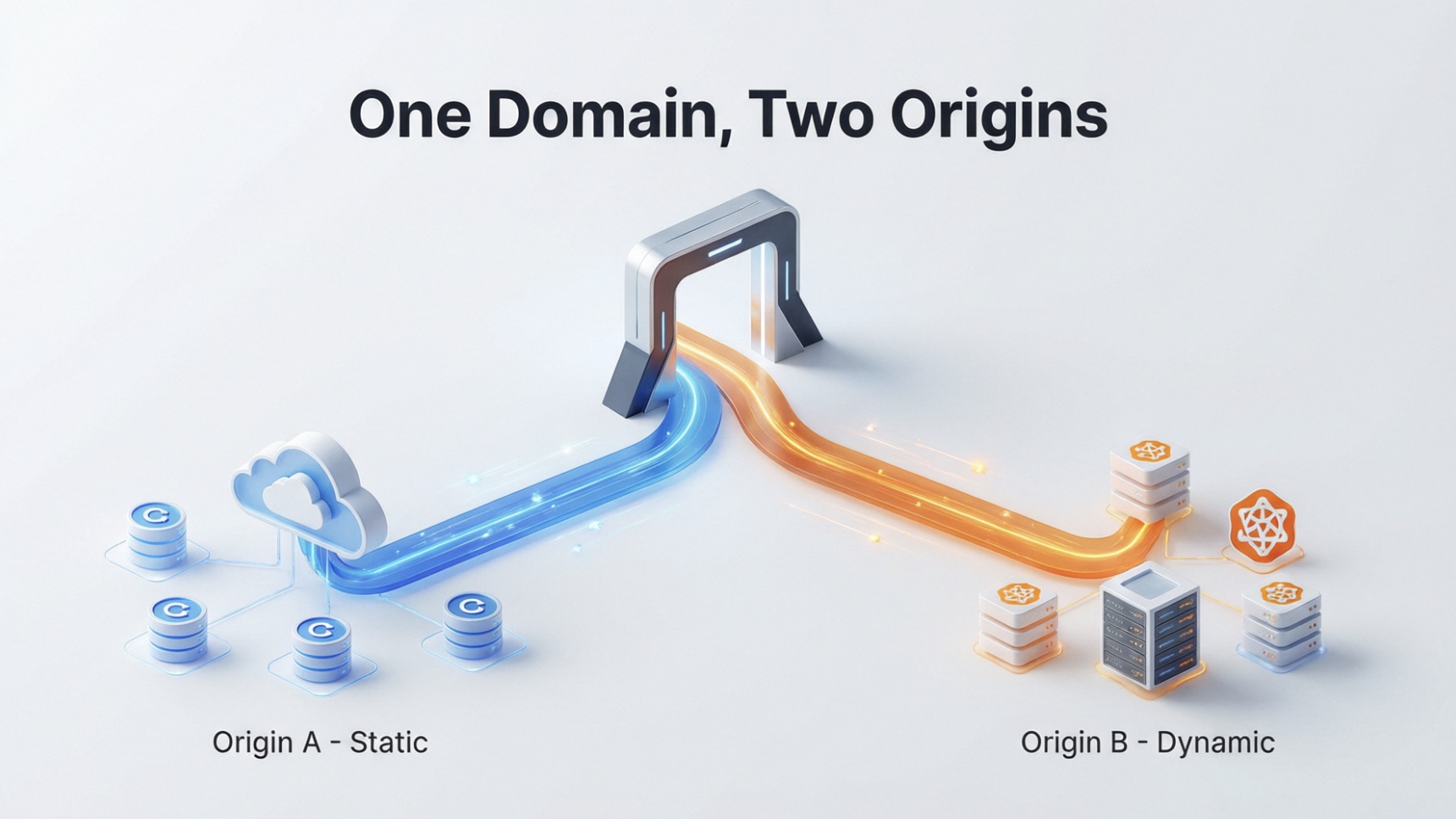
The most common question I get from ESA customers: "can I serve static files from OSS and route API calls to ECS - under a single domain?" This PoC proves the answer is yes, and shows exactly how.
 May 28, 2026
May 28, 2026
Alibaba Cloud launches Qwen Cloud, an AI-native platform built for AI Agents with multi-modal model access.

 May 28, 2026
May 28, 2026
This article analyzes the root causes of the 18-year-old Nginx vulnerability (CVE-2026-42945) and explores the evolution of gateway security architecture.

 May 28, 2026
May 28, 2026
This article examines multi-step orchestration on Alibaba Cloud Serverless Workflow.

 May 27, 2026
May 27, 2026
This article examines index lifecycle, shard allocation, and search request processing on Alibaba Cloud Elasticsearch and the design decisions that determine cluster performance at scale.

 May 27, 2026
May 27, 2026
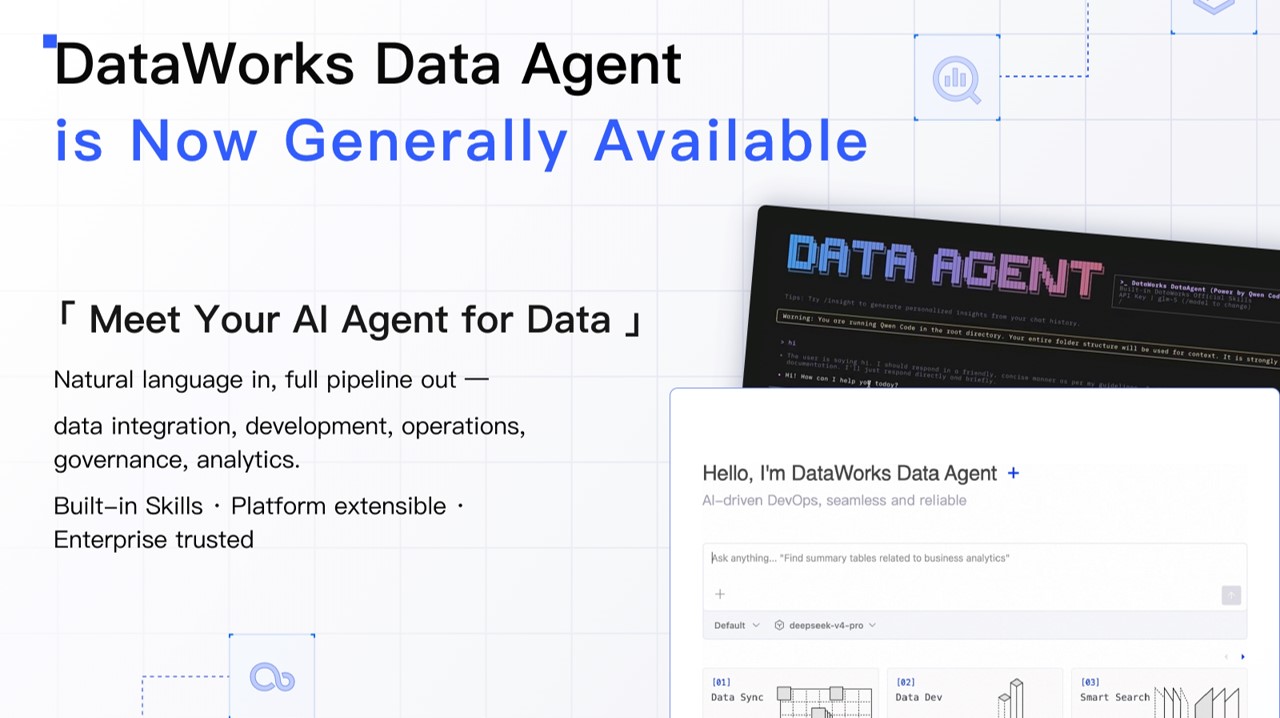
DataWorks Data Agent is now GA, offering natural language-driven automation for end-to-end data development with enterprise-grade security.
 May 27, 2026
May 27, 2026
Alibaba Cloud is deepening its push into agentic AI with a full-stack ecosystem designed to help businesses build, deploy and manage AI agents more easily.

 May 27, 2026
May 27, 2026
This article examines the agent architecture, detection engines, response workflows, and configuration decisions behind Alibaba Cloud Security Center.

 May 27, 2026
May 27, 2026
This article introduces how SysOM Agent uses AI to pinpoint Pod memory alert root causes in 30 seconds via a single conversation.

 May 27, 2026
May 27, 2026
This article shows how ACK AI Assistant and SysOM MCP enable single-conversation, full-stack cloud-native memory troubleshooting via Model Context Protocol.

 May 27, 2026
May 27, 2026
Empower AI Agents with Hologres CLI & Skills. JSON-first output, 6-layer safety, and auto-optimization.

 May 27, 2026
May 27, 2026
Choosing how to deploy a large language model in production is one of the most consequential — and confusing — decisions an AI team can make.
 May 26, 2026
May 26, 2026
This article examines how credential vaulting, session brokering, command policy enforcement, and audit forwarding combine in Alibaba Cloud Bastionhos...

 May 26, 2026
May 26, 2026
Alibaba Cloud today unveiled a suite of advanced model, infrastructure upgrades, AI-native platform and AI agent products for its global customers.

 May 26, 2026
May 26, 2026
This article examines how Alibaba Cloud Anti-DDoS Pro mitigates volumetric distributed denial-of-service attacks through the traffic diversion model, ...

 May 26, 2026
May 26, 2026
This article introduces Alibaba Cloud's Agent Infra, a comprehensive product matrix unveiled at the 2026 Summit to address the full lifecycle challeng.

 May 26, 2026
May 26, 2026
This article examines the failure modes that intelligent traffic management is designed to address, including regional outages, geographic latency var...

 May 26, 2026
May 26, 2026
This article introduces Alibaba Cloud's AI Agent Security Solution, addressing enterprise risks like prompt injection and offering robust mitigations for safe adoption.
 May 26, 2026
May 26, 2026
This article traces how a change moves from a developer commit to running, observable production software on Alibaba Cloud, and the architectural decisions that shape each transition along the way.
 May 25, 2026
May 25, 2026
Top Posts
01
02
03
04
01
02
03
04
05
06
07
08
09
10
Top Bloggers
| Ranking | Blogger | Posts |
| 1 | PM - C2C_Yuan | 7 |
| 2 | Alibaba Cloud Community | 5 |
| 3 | Alibaba Cloud Native Community | 5 |
| 4 | Alibaba Cloud Big Data and AI | 2 |
| 5 | OpenAnolis | 2 |
| 6 | CloudSecurity | 1 |
| 7 | Farruh | 1 |
| 8 | Bella - Cloud Communication | 1 |
| 9 | Bryan, Zhang | 1 |
| 1 | PM - C2C_Yuan | 24 |
| 2 | Alibaba Cloud Community | 19 |
| 3 | Alibaba Cloud Native Community | 18 |
| 4 | ApsaraDB | 15 |
| 5 | Kalpesh Parmar | 14 |
| 6 | Alibaba Cloud Big Data and AI | 3 |
| 7 | OpenAnolis | 2 |
| 8 | Neel_Shah | 2 |
| 9 | Bryan, Zhang | 2 |
| 10 | ESA-bigfan-Fred | 2 |
285 posts | 26 followers
71 posts | 157 followers
107 posts | 10 followers
109 posts | 2 followers
56 posts | 8 followers
22 posts | 177 followers
36 posts | 33 followers
53 posts | 10 followers
39 posts | 6 followers
24 posts | 5 followers
Drop us an email at community@list.alibaba-inc.com
Subject Line: Application for Alibaba Cloud Blog Author with these information:
We will review your submission and get back to you as soon as possible. We look forward to receiving your application.









